Welcome to our third in a series of three articles on cybersecurity. In this article, we engage a panel of experts to discuss practical steps organizations can take to improve Internet security for the overall office and remote workers.
The Tasker Blog: In your opinion, what practical, immediate steps should organizations take to reduce the threat of ransomware, phishing, and other cyber threats?
Security Panel: Organizations, who haven’t done so already, should immediately implement Multi-factor Authentication to provide layered security to vulnerable data and systems and also require administrators to use two separate accounts:
- Standard, normally privileged accounts for day-to-day use
- Administrator accounts for tasks that require special permissions, such as installing software
The Tasker Blog: What long-term strategies should organizations implement to improve Internet security?
Security Panel: Implementing an account disablement policy and account audits are two critical strategies for improving Internet security.
- Setting an account disablement policy, as detailed in this article from Microsoft, involves setting a threshold for the number of times an incorrect password can be entered before the system disables the account. This prevents cybercriminals from using a trial & error process (manual or automated) to identify user login credentials
- Account audits. Organizations should implement an ongoing process for validating user accounts and user account security and for reviewing activity logs to identify any potentially abnormal/harmful activities
The Tasker Blog: What steps can remote workers take to improve security in their home offices? How can organizations support this effort?
Security Panel: Remote workers must get in the habit of immediately applying operating system and application patches as soon as they become available. Additionally, users need to stay on top of current cybersecurity best practices by regularly taking phishing awareness training courses, such as the publicly available Phishing Awareness – DoD Cyber Exchange.
Organizations can support this effort by employing Mobile Application and Mobil Device Management, such as provided by Microsoft Intune. Additionally, organizations can perform Attack simulations and Attack simulation training via Microsoft 365 Defender to train employees on how to best respond to cyber threats.
The Tasker Blog: How should organizations and individuals respond to a “successful” ransomware attack?
Security Panel: We’ll defer to what Dave Truitt said in the previous Security Blog article (summarized below).
“Unfortunately, there are only a few ways to handle this scenario and most companies have no choice but to negotiate a settlement with the cybercriminals. Once your network is compromised and you have no access to your data, a company must simply do what is necessary to get back up and running. Having said that, it should give every company the determination to take proactive measures to ensure they never face an attack that has the potential to severely impact its future.“
The Tasker Blog: How critical is it for software product companies to build security into their products?
Security Panel: Everyone I talk to agrees that code reviews are a must and useful not only for identifying logic issues but for knowledge sharing across a team. However, do companies always build enough time in their development cycles to properly perform code reviews?
When teams conduct code reviews, it is easy to identify solutions that create common security vulnerabilities, such as SQL injection, command injection, cross-site scripting (XSS), unsafe file access, remote code execution, cross-site forgery, open redirects, and session manipulation.
Ok, the previous comment is a bit tongue in cheek, but seriously that list is just the tip of the iceberg. With that, do all companies know how to spot algorithms that implement even that short list of code vulnerabilities? Probably not, and most certainly not when third-party and/or open-source components are involved. It is very difficult for teams to identify these vulnerabilities in minified and obfuscated third-party components/solutions.
Also, every company believes they have the very best and brightest developers. While this may very well be true, all developers are human and make mistakes. For example, developers may occasionally, dare I say, use code snippets found on the Internet!
Software product companies must actively combat the common, emphatic arguments “But it works!” and “It’s what the customer wants!” and always address functionality that contains a known vulnerability.
The very last thing a software product company needs is to have a customer identify a security breach in their systems and determine the breach originated from your company’s product.
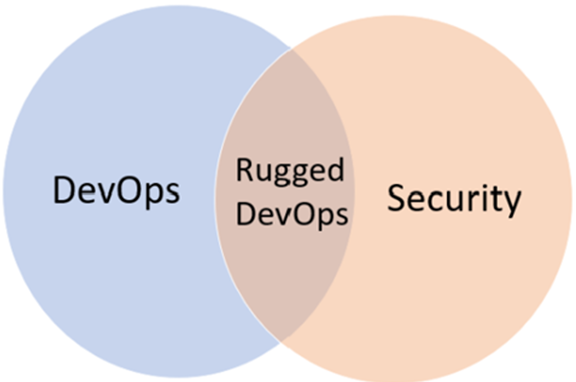
So, how critical is it that companies build security into their products? Extremely critical! However, I think it’s imperative to define what “building security into” means. To me, this means employing DevOps. On top of that, it is critical to employ code security scanning within DevOps pipelines and achieving Rugged DevOps, otherwise known as DevSecOps.
We hope you have found our series on cybersecurity informative and useful. There is much more to discuss on this subject, and we look forward to continuing our discussion in a future article.
In the meantime, if you are interested in learning more about our secure suite of Task Management, Document Management, and Document Generation apps (available on the ServiceNow platform), get in touch with us via the DTech Apps website.